According to HotHardware, security researchers at Securonix have uncovered a new malware campaign, dubbed PHALT#BLYX, targeting Windows users. The attack starts with a phishing email disguised as a booking.com reservation cancellation notice. If a victim clicks the link, they’re taken to a fake site that eventually displays a full-screen, counterfeit Windows Blue Screen of Death error. This fake BSOD provides instructions that, when followed, run a command to install malicious software. Once installed, the malware gains high-level access, logs keystrokes, records screens, and can even deploy a cryptocurrency miner. The attackers are believed to be timing this to exploit busy travel periods like the holidays and events such as CES.
The BSOD Bait-and-Switch
Here’s the thing that makes this attack so clever: it weaponizes a universal symbol of PC panic. Everyone who’s used Windows has seen the Blue Screen of Death. It triggers an immediate, visceral “oh no” reaction. The attackers are counting on that moment of panic to short-circuit your better judgment. You’re not thinking about phishing links anymore; you’re thinking your computer is broken and you need to fix it. So when the fake error gives you a set of steps to “resolve” the issue, the temptation to just follow them is huge. It’s social engineering that bypasses your brain’s security center by pretending to be a system-level problem.
Beyond The Initial Infection
But the fake BSOD is just the opening act. The real show starts once the malware, called ClickFix, is on your machine. It doesn’t just sit there. It works to get administrator privileges and make sure it survives a reboot. That’s how you get persistent threats. Then, it gets to work. Keylogging? Check. Screen recording? Check. That’s a one-two punch for stealing absolutely everything: passwords, bank details, confidential documents you have open. And as if that weren’t enough, the attackers can also turn your computer into a crypto mining zombie. So they’re not just stealing your data; they’re stealing your computer’s processing power and running up your electricity bill. Talk about adding insult to injury.
Why This Still Works
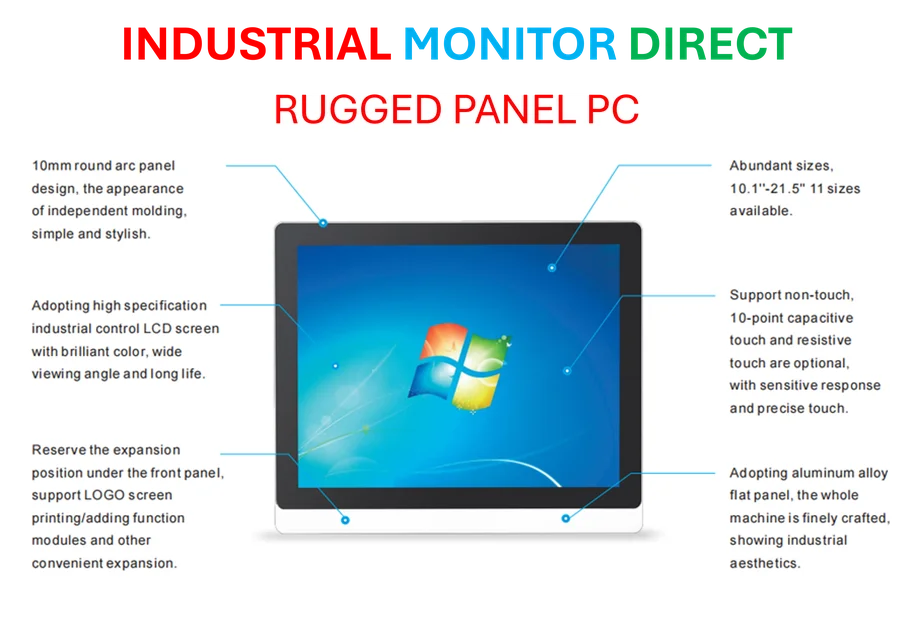
Look, we all know we shouldn’t click sketchy links in emails. But these campaigns are getting scarily good at mimicking legitimate services—in this case, booking.com—and exploiting timely scenarios. A travel booking cancellation right during the holiday or CES travel crunch? That’s going to get someone’s attention. It preys on urgency and legitimate concern. This is a reminder that the human element is still the weakest link in security. The tech can be sophisticated, but the hook is always basic psychology: fear, urgency, or curiosity. For businesses relying on critical computing hardware, from standard workstations to specialized industrial panel PCs, the principle is the same. The entry point is often a person, not a firewall. And that’s why continuous user education is just as important as any antivirus software.
The Basic Defense Playbook
So what do you do? The advice feels old, but it’s gold because it works. Be supremely skeptical of unsolicited emails, especially ones with links or that create a sense of panic. Hover over links to see where they *really* go. If you get a system error from a website, that’s a massive red flag. A real Windows BSOD doesn’t come from your web browser. Basically, if something feels off, it probably is. Close the browser. Restart your computer normally. And maybe take it as a sign that it’s time to check your backups and make sure your security software is up to date. It’s a constant game of cat and mouse, but the mice are getting better at wearing cat costumes.